A technical code fragment has been discovered on the New York Times website, revealing backend security and tracking mechanisms used by the publication. The code snippet contains various technical parameters including runtime configurations, client identification numbers, hash values, and security tokens. The fragment shows a variable declaration with multiple data points: a runtime type marked as 'c', a client ID string 'AHrlqAAAAAMAvAEsEb9w-s8AeVgFqA', and a hash value '499AE34129FA4E4FABC31582C3075D'. The code also includes a session size parameter of 17,439 bytes and references to geo-location captcha delivery systems hosted at 'geo.captcha-delivery.com'. Additionally, the fragment contains an encrypted security token and cookie data used for user session management and authentication purposes. This type of code is typically used by major news websites to manage user interactions, prevent automated access, and ensure secure content delivery. The presence of such technical elements highlights the complex infrastructure required to operate a major digital news platform like the New York Times, where security measures and user tracking systems work together to maintain site functionality and protect against unauthorized access.
Latest article
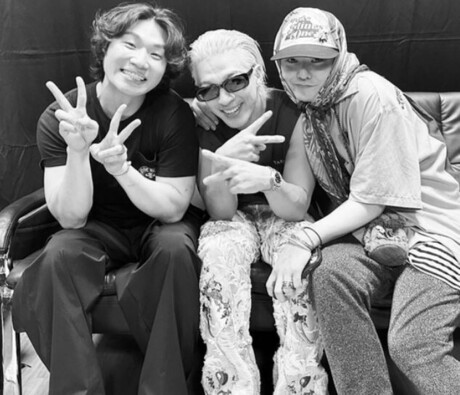
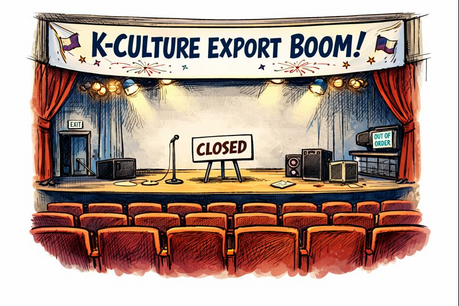
- Stray Kids’ Global Momentum Continues With Fashion Week Appearances and Fan Event Teasers
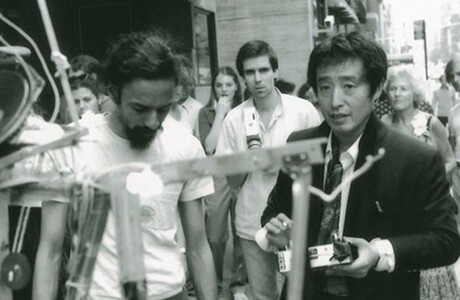
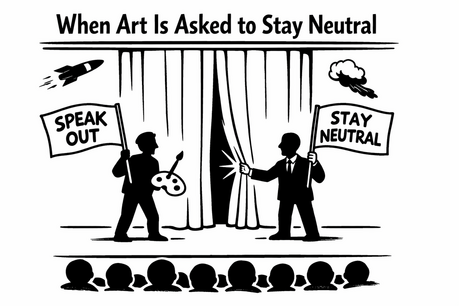
- South Korea’s Art World at a Crossroads: Celebrity Influence, Civic Engagement and Institutional Power
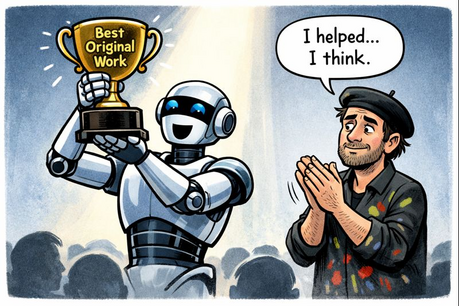
- AI Art’s Legitimacy Crisis: Who Owns Creativity in the Age of Algorithms?
- What Should Gwanghwamun Say — and in Whose Script?
- Gwanghwamun Nameboard Debate Rekindles Questions of Identity in South Korea
- BTS Returns With ARIRANG, Signaling a New Phase of Global Expansion
- Big Bang to Launch 20th Anniversary World Tour; YG Unveils Major Comeback Plans
- Who Is the Artist?