A technical security system has been activated on a website, displaying code-related information that appears to be part of an automated security verification process. The system generated various technical parameters including routing identifiers, session tokens, and host verification data. This type of activation typically occurs when websites implement security measures to protect against automated traffic or potential security threats. The displayed information includes encrypted hash values, client identification numbers, and cookie authentication data that are commonly used in web security protocols. Such security implementations have become increasingly common as websites work to maintain safe browsing environments for their users while preventing unauthorized automated access attempts.
Latest article
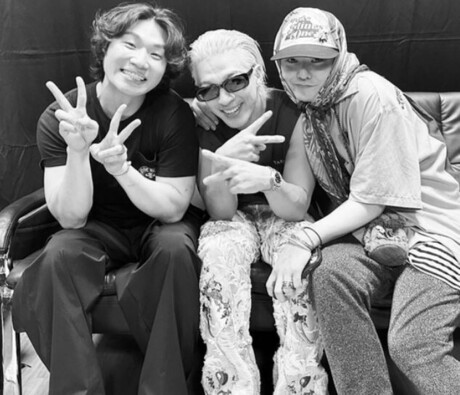
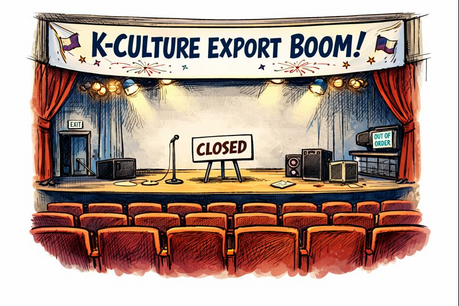
- Stray Kids’ Global Momentum Continues With Fashion Week Appearances and Fan Event Teasers
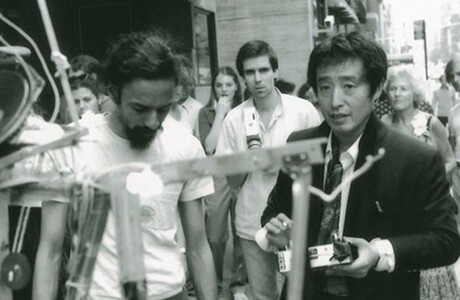
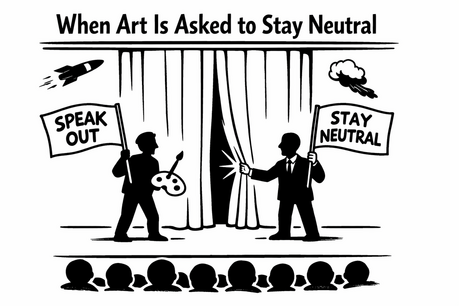
- South Korea’s Art World at a Crossroads: Celebrity Influence, Civic Engagement and Institutional Power
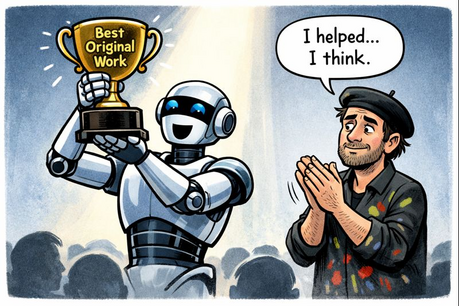
- AI Art’s Legitimacy Crisis: Who Owns Creativity in the Age of Algorithms?
- What Should Gwanghwamun Say — and in Whose Script?
- Gwanghwamun Nameboard Debate Rekindles Questions of Identity in South Korea
- BTS Returns With ARIRANG, Signaling a New Phase of Global Expansion
- Big Bang to Launch 20th Anniversary World Tour; YG Unveils Major Comeback Plans
- Who Is the Artist?